Buildkite is a CIaaS tool that offers fast, secure, and scalable CI on private infrastructure that can be managed from a nifty web UI. It integrates seamlessly into MacStadium’s Orka, a Docker and Kubernetes-driven orchestration layer that offers virtualized macOS build machines running on genuine Apple hardware.
Today, we’ll take a look at using Buildkite to connect a GitHub account with Orka, and running our first static CI/CD pipeline.
Connect Buildkite to GitHub
First, you’ll need to let Buildkite have access to your resources on GitHub. To do so, in the Buildkite UI navigate to Settings and click the Repository Providers tab on the left. Click on GitHub (connect to a GitHub account). Select your account, enter your credentials, and Buildkite will be able to see this repository.
Install and Configure the Buildkite Agent
Next, spin up a macOS VM in Orka, and install the Buildkite agent on the virtual machine. To do so, first, install Homebrew on the VM, and then run:
brew install buildkite/buildkite/buildkite-agent Finally, configure the Buildkite agent token, like so:
sed -i '' "s/xxx/INSERT-YOUR-AGENT-TOKEN-HERE/g" "$(brew --prefix)"/etc/buildkite-agent/buildkite-agent.cfgDefine a Pipeline
Next, in the Buildkite UI, you’ll need to define a pipeline. Provide a name for the pipeline, and select the repository you’d like to target. We’ll generate SSH keys shortly, so you can leave SSH as the checkout method. Note that when a GitHub repository is selected, the Auto-create webhooks checkbox is checked automatically.

The steps for your workflow can either be defined in YAML, or via the UI like so:

Generate SSH Keys
In order for Buildkite to check out our code, we’ll need to use SSH keys to authenticate. On your macOS VM, run the following commands to generate the required SSH keys. Note that no passphrase is being set.
administrator@2540 .ssh % ssh-keygen -t ed25519 -C "jeff.d.vincent@gmail.com" Generating public/private ed25519 key pair. Enter file in which to save the key (/Users/administrator/.ssh/id_ed25519): Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /Users/administrator/.ssh/id_ed25519. Your public key has been saved in /Users/administrator/.ssh/id_ed25519.pub. The key fingerprint is: SHA256:MCb+aBPKRNNlDitvshe+k9iTleya+MMW+hn3yv2VU84 myemail@email.com The key's randomart image is: +--[ED25519 256]--+ | . o | | . * | | + + = | | . = o o | | o *. .S . | | o *.=+ = | | +=B*o + E | | o+XO.o . . | | .+B=o.o.. | +----[SHA256]-----+ administrator@2540 .ssh % ls id_ed25519 id_ed25519.pub known_hosts administrator@2540 .ssh % cat id_ed25519.pub ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIL6r8wzZ5VtB4F1t9N7Xsnelhbv8+1voF4a5EocKOROH myemail@email.comAdd Your Public Key to GitHub
In your target GitHub repository, navigate to Settings and then click the Deploy Keys tab on the left. Give your key a name, and paste in the contents of the .pub file that you created, and finally click Add Key.

Test Your Pipeline
Buildkite pipelines target the branch “master” by default. To change this target to “main”, simply navigate to Pipelines and then click on your new pipeline. Then click on Pipeline Settings, update the default branch, and click Save Default Branch.

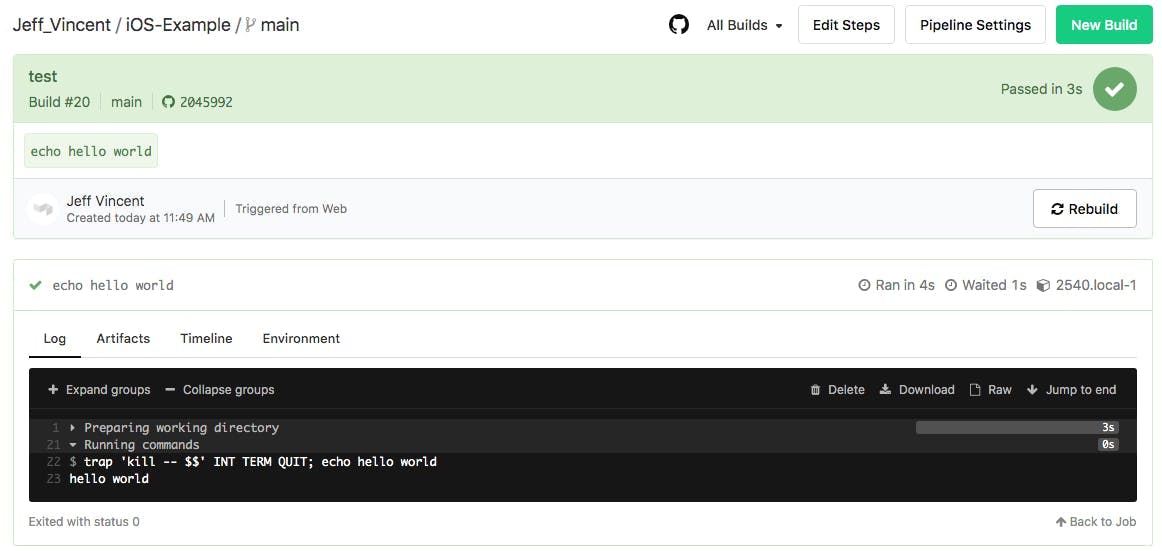
Then, simply click New Build, enter a required message, and click Create Build. You will then be able to track your build’s execution in the Buildkite UI, as shown in the following:
TL;DR
Buildkite is a fast, secure CI-aaS provider that integrates with GitHub, and that offers a viable option for cloud-based, iOS CI. Above, we covered the steps to getting your first static Buildkite + GitHub pipeline integrated with MacStadium’s Orka. To learn more about ephemeral setup, check out the docs.
Share this article
Orka, Orka Workspace and Orka Pulse are trademarks of MacStadium, Inc. Apple, Mac, Mac mini, Mac Pro, Mac Studio, and macOS are trademarks of Apple Inc. The names and logos of third-party products and companies shown on the website are the property of their respective owners and may also be trademarked.
©2025 MacStadium, Inc. is a U.S. corporation headquartered at 3340 Peachtree Rd NE, Suite 2330, Atlanta, GA 30326. MacStadium, Ltd. is registered in Ireland, company no. 562354.